Ransomware has changed a lot since it first started locking peoples computers for small payments. By 2026 attackers are using Ransomware 3.0 which’s a new kind of malware that uses artificial intelligence. Ransomware 3.0 does not just encrypt data it also steals information threatens to damage a companys reputation and targets cloud systems. This makes Ransomware 3.0 one of the cyber threats we face today.

- What is Ransomware 3.0?
Ransomware 3.0 is a type of malware that combines encryption, data theft and extortion. These attacks are different from versions because they often:
- Steal sensitive data before encrypting it.
- Threaten to leak information if the ransom is not paid.
- Target cloud. Software platforms.
- Use intelligence to adapt and avoid detection.
- Why It Matters in 2026
Ransomware attacks are happening over the world affecting hospitals, governments and big companies.
The financial impact is huge with average ransom demands exceeding millions of dollars.
Data leaks can harm a companys reputation. Affect their compliance with regulations.
Critical infrastructure is also being targeted, which is a threat to security.
- Common Attack Vectors
Attackers use phishing emails that are crafted using intelligence to trick employees.
They also exploit Remote Desktop Protocol to gain access.
Cloud misconfigurations are another way attackers can exploit cloud defenses.
Supply chains can be vulnerable too with vendors and contractors becoming entry points for attacks.
- Real-World Examples
The Colonial Pipeline attack in 2021 disrupted the fuel supply across the United States.
There were also healthcare attacks between 2024 and 2025 that forced hospitals to delay surgeries due to Ransomware 3.0.
Municipal governments around the world have been crippled by encrypted systems.
- Defensive Best Practices
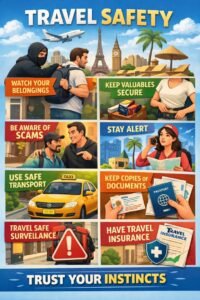
Using a Zero Trust Architecture can help verify users and devices
Multi-Factor Authentication can prevent theft.
Regular backups should be stored offline to resist Ransomware 3.0 attacks that target cloud systems.
Employee training is important to raise awareness about phishing and social engineering.
Having incident response plans in place can help with recovery.
- Emerging Trends in 2026
Artificial intelligence is being used to power defense systems that can detect Ransomware 3.0 behavior early.
Blockchain-based backups are being used to prevent tampering.
Cyber insurance policies are evolving to require compliance with security standards.
Governments are collaborating to share intelligence and combat Ransomware 3.0 groups.
- Case Study: Healthcare Sector
Hospitals face risks, including patient data, IoT medical devices and critical operations. A Ransomware 3.0 attack can put lives in danger. By adopting Zero Trust, offline backups and artificial intelligence monitoring healthcare organizations can reduce risks. Comply with privacy regulations.
- Building a Ransomware-Resilient Culture
Technology alone cannot stop Ransomware 3.0. Employees need to understand the risks, practice secure habits and report activity. Leadership must prioritize Ransomware 3.0 defense as a business imperative.
- Checklist, for Ransomware Defense
[ ] Enforce Multi-Factor Authentication
[ ] Apply Zero Trust principles
[ ] Maintain offline backups
[ ] Train employees regularly
[ ] Audit systems quarterly
Ransomware 3.0 is the most advanced and dangerous evolution of cyber extortion. In 2026 organizations must combine technology, policy and culture to defend against Ransomware 3.0. By using Zero Trust, intelligence-powered monitoring and resilient backup strategies businesses can withstand the next wave of Ransomware 3.0 attacks.
contact us more https://meeqam.com/contct us/